Replace polite CISO interest with real pipeline.
Replace polite CISO interest with real pipeline.
Replace polite CISO interest with real pipeline.
Replace polite CISO interest with real pipeline.
Only target people with a real pain. Make your messaging count – no more ghosting or stalling.
Only target people with a real pain. Make your messaging count – no more ghosting or stalling.
Only target people with a real pain. Make your messaging count – no more ghosting or stalling.
Know exactly what to say to hook prospects, find out who is a buyer and move on to a deal.
Know exactly what to say to hook prospects, find out who is a buyer and move on to a deal.
Know exactly what to say to hook prospects, find out who is a buyer and move on to a deal.
Develop repeatable winning outreach and get ready to scale.
Develop repeatable wining outreach and get ready to scale.
Develop repeatable winning outreach and get ready to scale.
The Problem
Why most cybersecurity GTM feels like an uphill struggle – even with a good product?
Why most cybersecurity GTM feels like an uphill struggle – even with a good product?
Why most cybersecurity GTM feels like an uphill struggle – even with a good product?
Client profile fails in outreach, despite looking OK on paper.
Broad firmographics and vague buyer definitions make targeting too broad and outreach generic.
What looks sensible on paper shows no pull in outreach.
Messaging doesn't work with real prospects.
Security buyers filter aggressively.
If your messaging doesn’t match their pain, definition of success, and urgency drivers, and doesn't address their perception of risk, it gets ignored.
No diagnostic signal telling you what specifically is broken.
Teams ship content, run outbound, and book calls – but deals stall and leads ghost. It's not clear what works and what doesn't.
There is no basis for iterative improvement.
Misleading early traction in an unscalable segment.
A few deals close, but only with significant customizations, long cycles, or heavy founder involvement.
This masks a GTM that won’t scale.
No clear disqual logic or its disciplined application.
Everything looks like a lead.
Time gets burned on prospects who were never going to buy.
GTM reuse in a new client segment.
What worked for fintechs doesn’t work for enterprises. Buyer roles, buying pressure, proof, messaging – they all change.
GTM has to be re-derived, not reused.
Client profile fails in outreach, despite looking OK on paper.
Broad firmographics and vague buyer definitions make targeting too broad and outreach generic.
What looks sensible on paper shows no pull in outreach.
Messaging doesn't work with real prospects.
Security buyers filter aggressively.
If your messaging doesn’t match their pain, definition of success, and urgency drivers, and doesn't address their perception of risk, it gets ignored.
No diagnostic signal telling you what specifically is broken.
Teams ship content, run outbound, and book calls – but deals stall and leads ghost. It's not clear what works and what doesn't.
There is no basis for iterative improvement.
Misleading early traction in an unscalable segment.
A few deals close, but only with significant customizations, long cycles, or heavy founder involvement.
This masks a GTM that won’t scale.
No clear disqual logic or its disciplined application.
Everything looks like a lead.
Time gets burned on prospects who were never going to buy.
GTM reuse in a new client segment.
What worked for fintechs doesn’t work for enterprises. Buyer roles, buying pressure, proof, messaging – they all change.
GTM has to be re-derived, not reused.
Client profile fails in outreach, despite looking OK on paper.
Broad firmographics and vague buyer definitions make targeting too broad and outreach generic.
What looks sensible on paper shows no pull in outreach.
Messaging doesn't work with real prospects.
Security buyers filter aggressively.
If your messaging doesn’t match their pain, definition of success, and urgency drivers, and doesn't address their perception of risk, it gets ignored.
No diagnostic signal telling you what specifically is broken.
Teams ship content, run outbound, and book calls – but deals stall and leads ghost. It's not clear what works and what doesn't.
There is no basis for iterative improvement.
Misleading early traction in an unscalable segment.
A few deals close, but only with significant customizations, long cycles, or heavy founder involvement.
This masks a GTM that won’t scale.
No clear disqual logic or its disciplined application.
Everything looks like a lead.
Time gets burned on prospects who were never going to buy.
GTM reuse in a new client segment.
What worked for fintechs doesn’t work for enterprises. Buyer roles, buying pressure, proof, messaging – they all change.
GTM has to be re-derived, not reused.
Client profile fails in outreach, despite looking OK on paper.
Broad firmographics and vague buyer definitions make targeting too broad and outreach generic.
What looks sensible on paper shows no pull in outreach.
Messaging doesn't work with real prospects.
Security buyers filter aggressively.
If your messaging doesn’t match their pain, definition of success, and urgency drivers, and doesn't address their perception of risk, it gets ignored.
No diagnostic signal telling you what specifically is broken.
Teams ship content, run outbound, and book calls – but deals stall and leads ghost. It's not clear what works and what doesn't.
There is no basis for iterative improvement.
Misleading early traction in an unscalable segment.
A few deals close, but only with significant customizations, long cycles, or heavy founder involvement.
This masks a GTM that won’t scale.
No clear disqual logic or its disciplined application.
Everything looks like a lead.
Time gets burned on prospects who were never going to buy.
GTM reuse in a new client segment.
What worked for fintechs doesn’t work for enterprises. Buyer roles, buying pressure, proof, messaging – they all change.
GTM has to be re-derived, not reused.
Solution
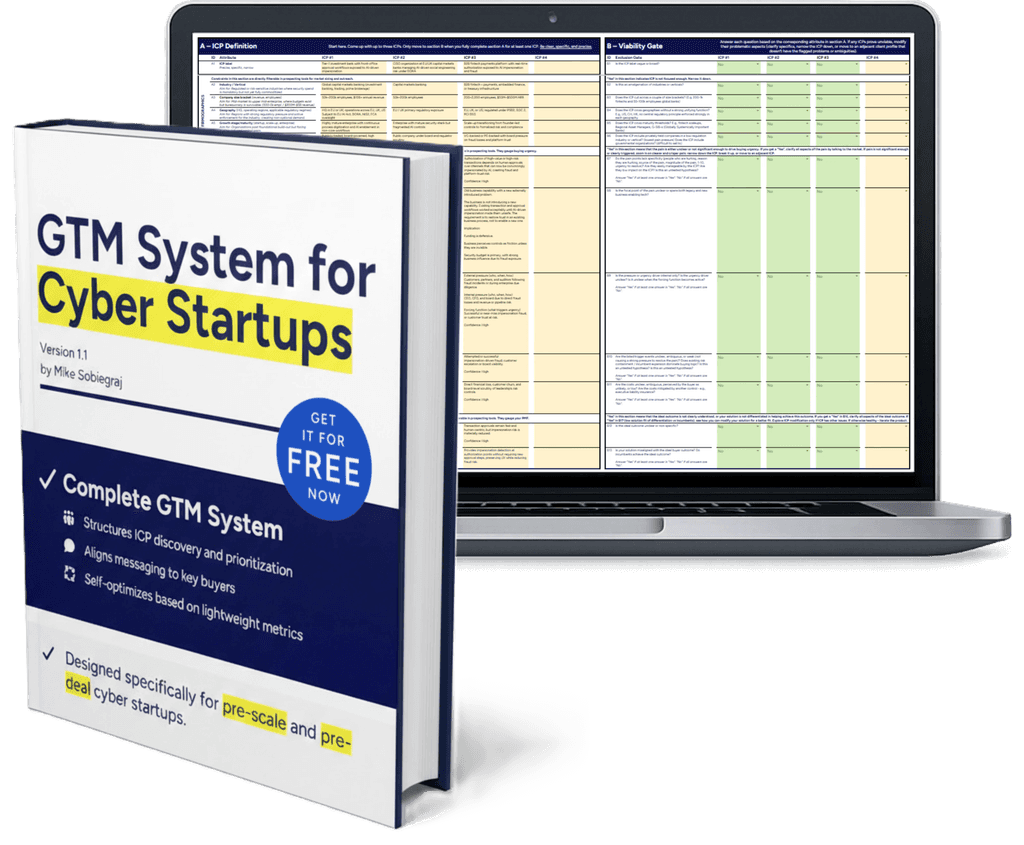
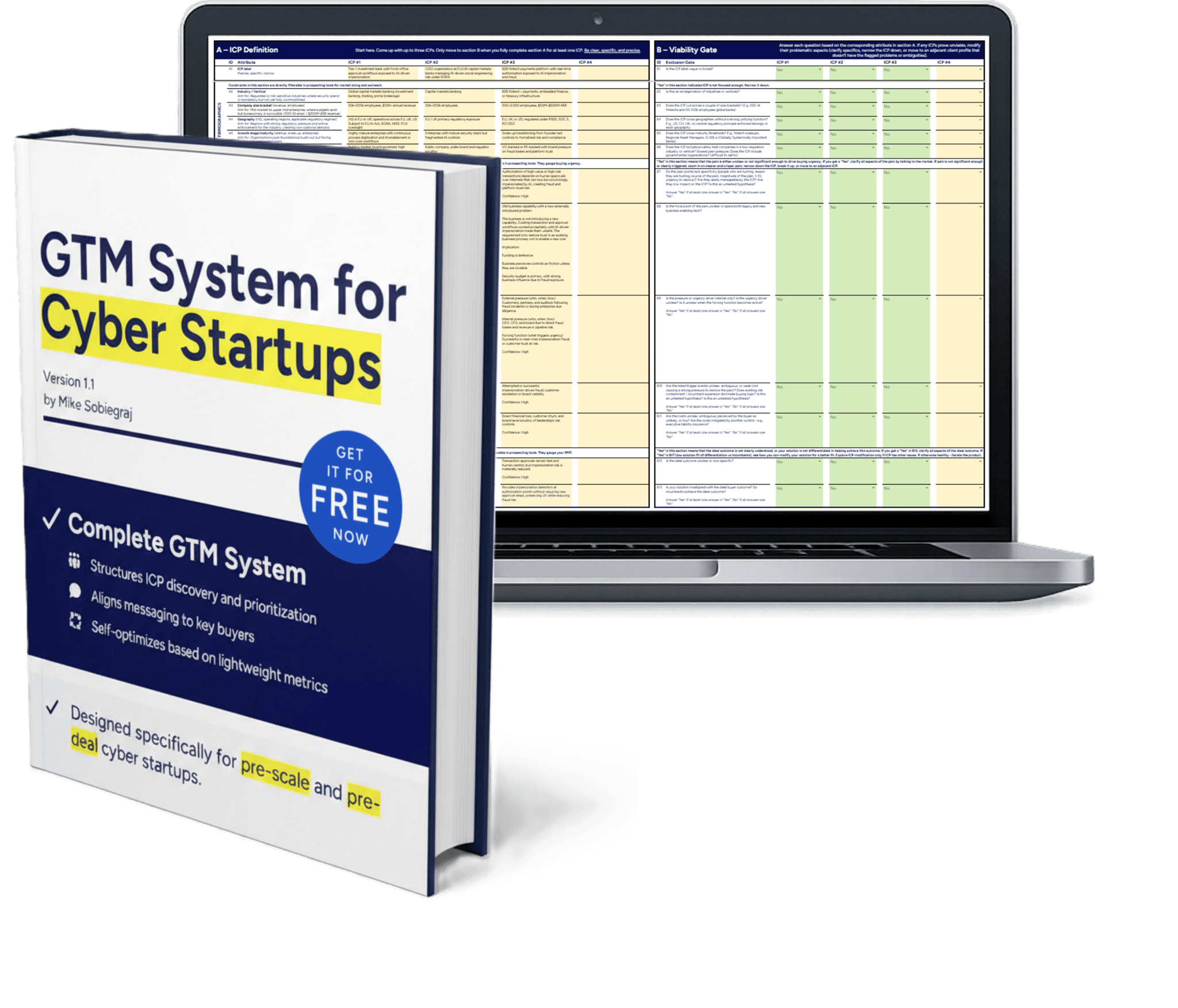
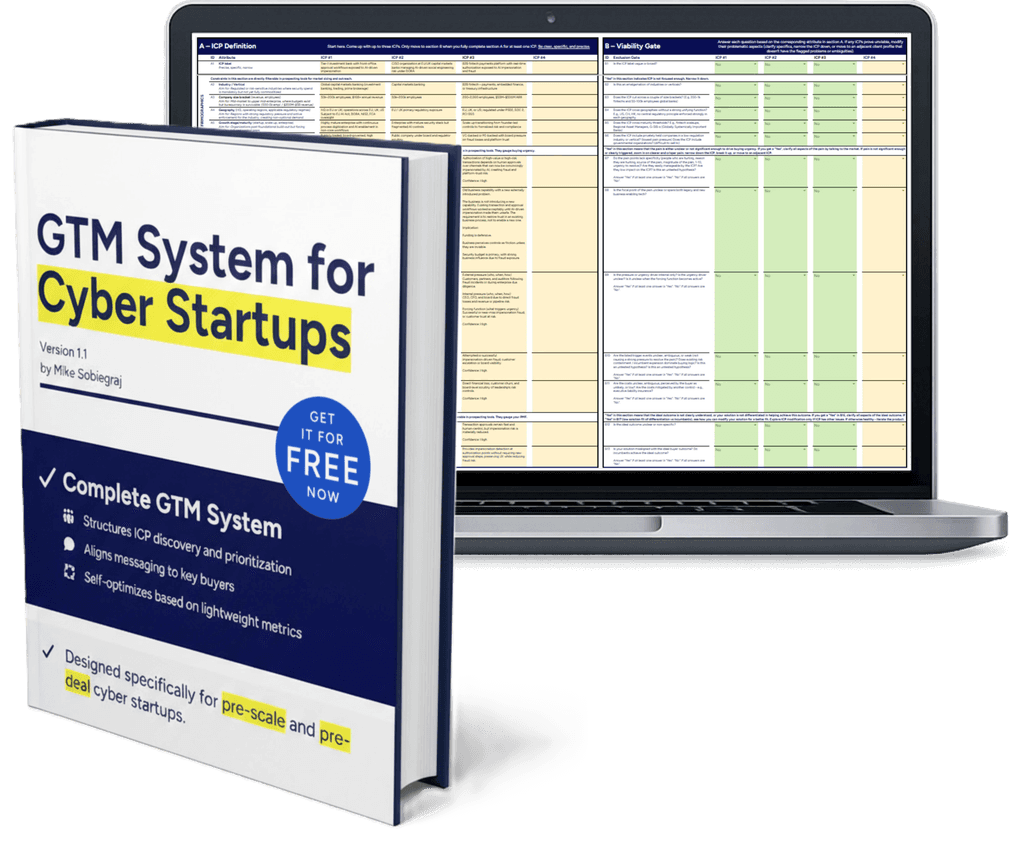
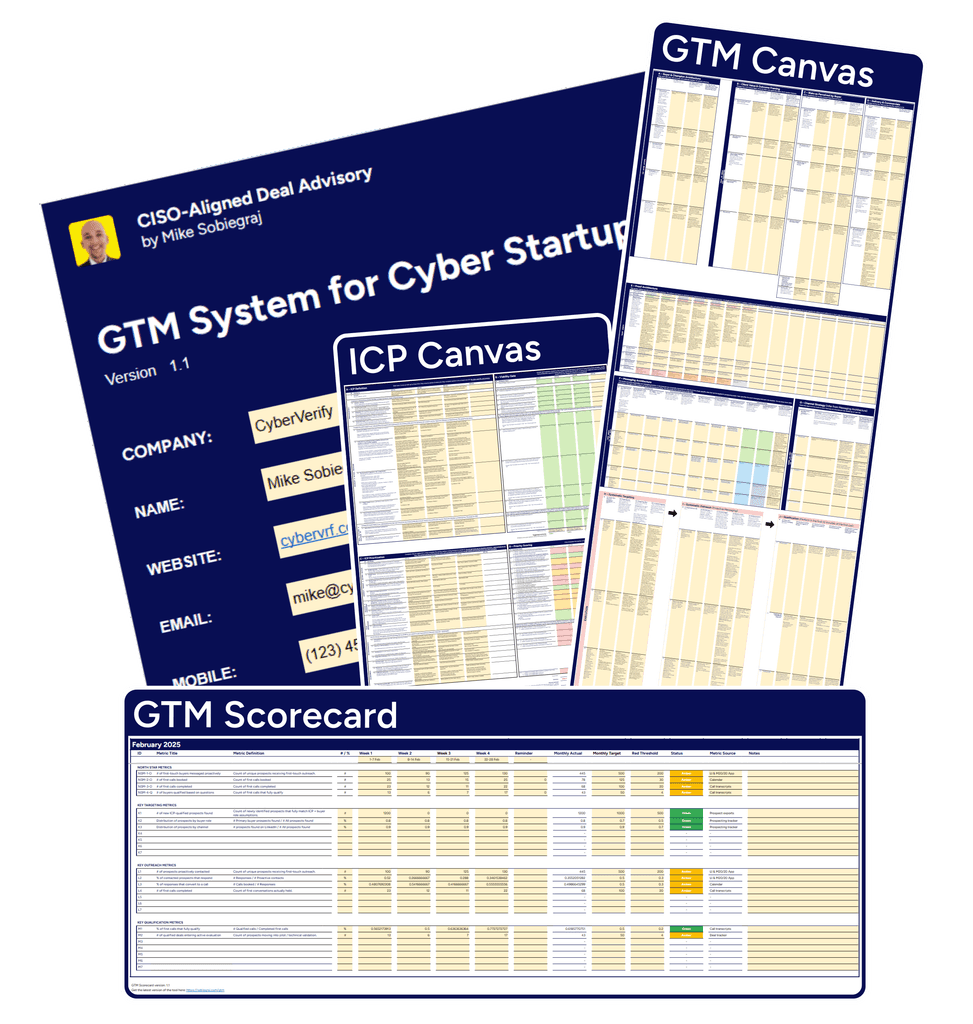
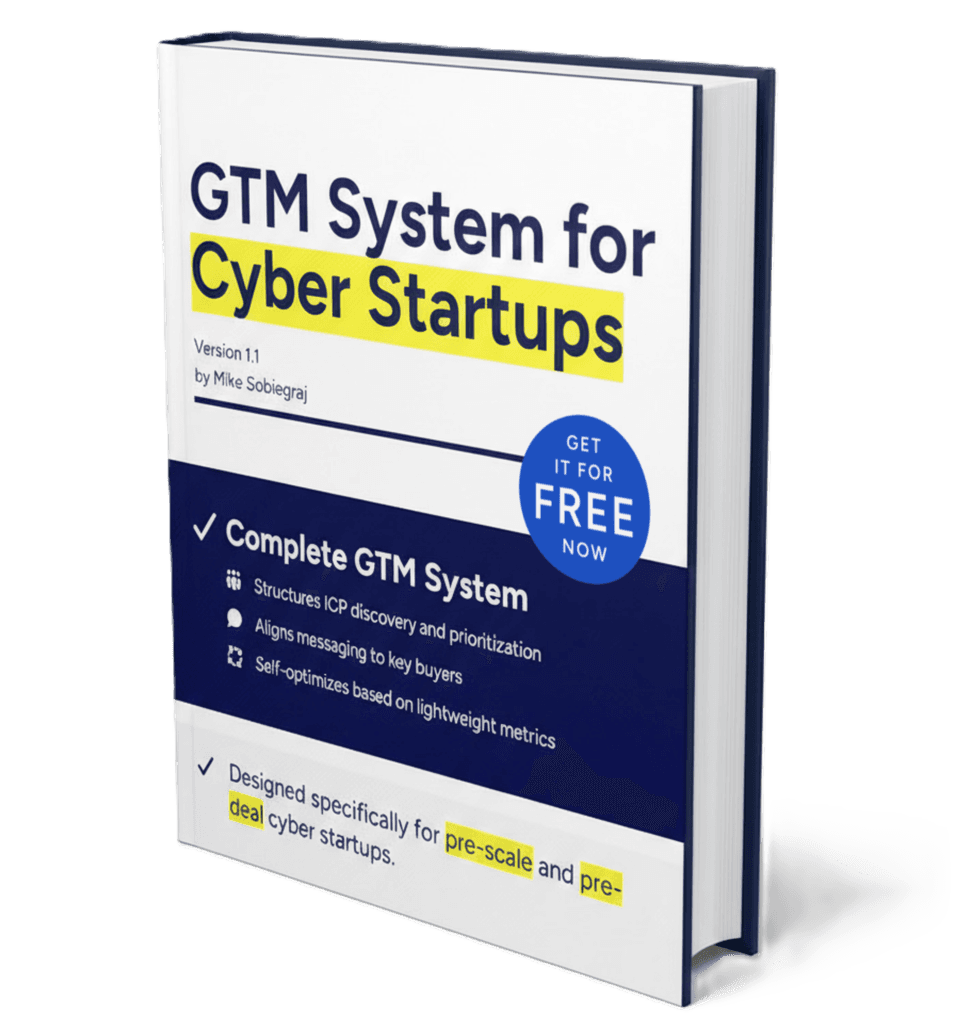
Complete GTM System for Cyber Startups.
Complete GTM System for Cyber Startups.
Complete GTM System for Cyber Startups.
Live-or-die for pre-scale startups.
Live-or-die for pre-scale startups.
Live-or-die for pre-scale startups.
Essential for any expansion to a new client segment.
Essential for any expansion to a new client segment.
Essential for any expansion to a new client segment.
DOWNLOAD AND START NOW
START NOW
DOWNLOAD AND START NOW
DOWNLOAD AND START NOW
The GTM System
The GTM System
The GTM System
The GTM System
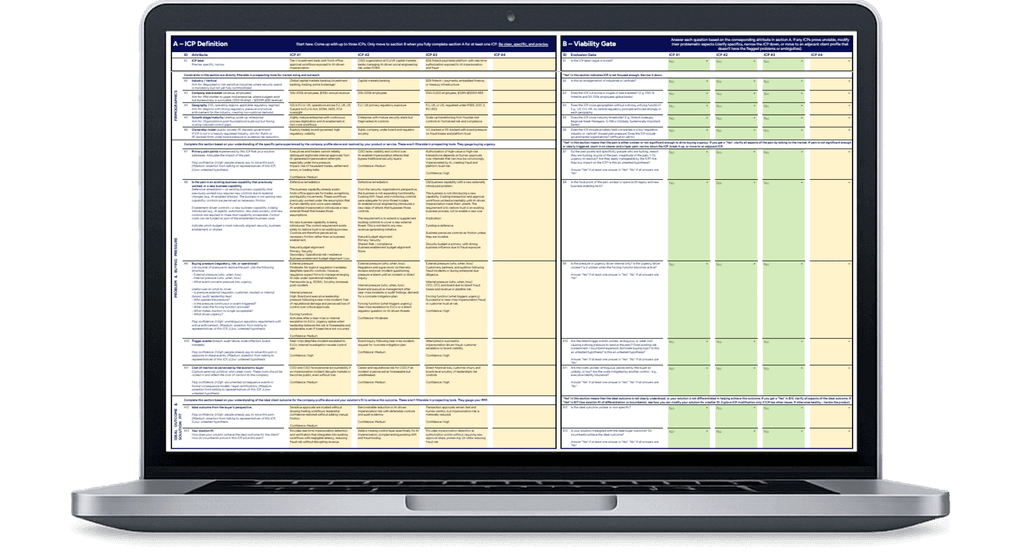
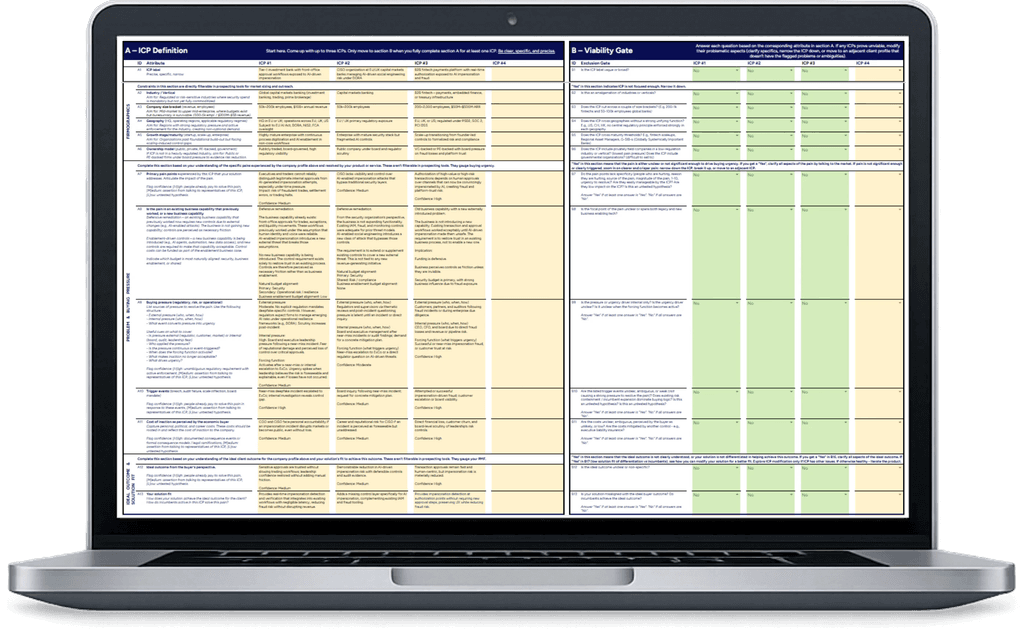
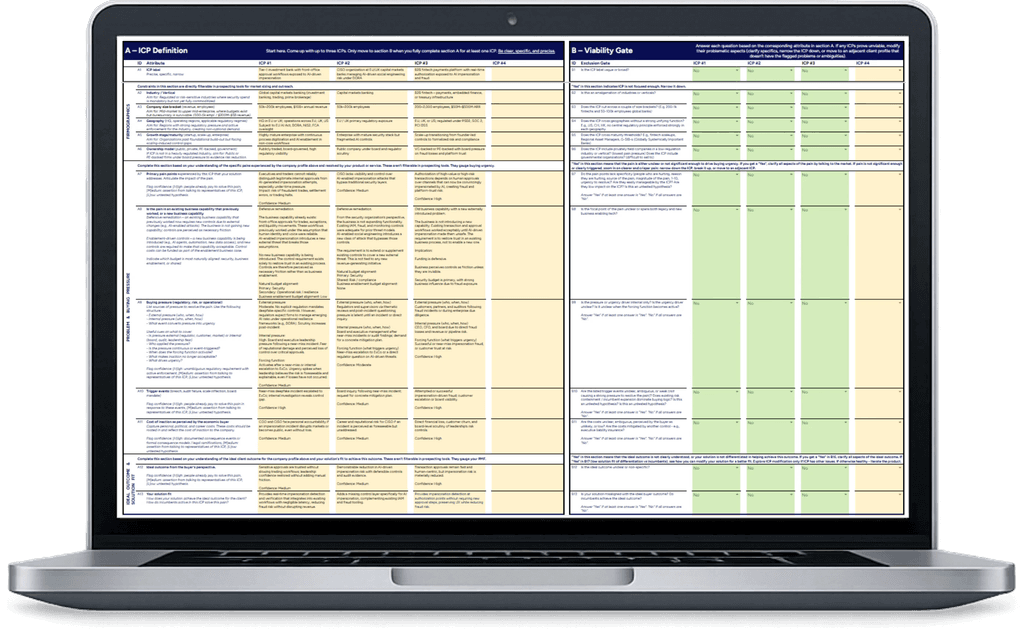
Step-by-step GTM system that forces clarity on ICP, buyers, pain & triggers, proof, messaging, outbound motion, and diagnostics – in the correct order.
It includes in-the-file buyer-side cues that guide you as you work.
Step-by-step GTM system that forces clarity on ICP, buyers, pain & triggers, proof, messaging, outbound motion, and diagnostics – in the correct order.
It includes in-the-file buyer-side cues that guide you as you work.
Step-by-step GTM system that forces clarity on ICP, buyers, pain & triggers, proof, messaging, outbound motion, and diagnostics – in the correct order.
It includes in-the-file buyer-side cues that guide you as you work.
Step-by-step GTM system that forces clarity on ICP, buyers, pain & triggers, proof, messaging, outbound motion, and diagnostics – in the correct order.
It includes in-the-file buyer-side cues that guide you as you work.
SEE HOW IT'S DONE
SEE HOW IT'S DONE
SEE HOW IT'S DONE
SEE HOW IT'S DONE
Example
Example
Example
See a specific, high-urgency ICP and targeted outbound for an example anti-AI-fraud startup. Narrowed down from a vague “CISO buyer”.
Use it as "what good looks like" when you develop your own system.
See a specific, high-urgency ICP and targeted outbound for an example anti-AI-fraud startup. Narrowed down from a vague “CISO buyer”.
Use it as "what good looks like" when you develop your own system.
See a specific, high-urgency ICP and targeted outbound for an example anti-AI-fraud startup. Narrowed down from a vague “CISO buyer”.
Use it as "what good looks like" when you develop your own system.
See a specific, high-urgency ICP and targeted outbound for an example anti-AI-fraud startup. Narrowed down from a vague “CISO buyer”.
Use it as "what good looks like" when you develop your own system.
ACCELERATE RAMP UP
ACCELERATE RAMP UP
ACCELERATE RAMP UP
ACCELERATE RAMP UP
Handbook
Handbook
Handbook
Get going in 15 minutes. The guide explains key GTM System mechanics.
It also spells out the most impactful buyer-side guidance – strong foundations for you to build on
from the start.
Get going in 15 minutes. The guide explains key GTM System mechanics.
It also spells out the most impactful buyer-side guidance – strong foundations for you to build on from the start.
Get going in 15 minutes. The guide explains key GTM System mechanics.
It also spells out the most impactful buyer-side guidance – strong foundations for you to build on from the start.
Get going in 15 minutes. The guide explains key GTM System mechanics.
It also spells out the most impactful buyer-side guidance – strong foundations for you to build on from the start.
About me
Built by someone who sat on the buyer’s side.
Built by someone who sat on the buyer’s side.
Built by someone who sat on the buyer’s side.
I spent years inside enterprise security and risk organizations, watching how vendors get evaluated, blocked, or approved.
I built this GTM System to package what I learned there for early-stage teams.
I spent years inside enterprise security and risk organizations, watching how vendors get evaluated, blocked, or approved.
I built this GTM System to package what I learned there for early-stage teams.



CISO-Aligned Sales
by Mike Sobiegraj
Former long-time enterprise cyber executive. I help cybersecurity sales leaders win enterprise deals by applying my firsthand knowledge of what moves deals forward – and what doesn’t.
Free value
One-pager
One-pager
One-pager
Tool
Handbook
Legal stuff
© 2025-2026 Mike Sobiegraj. All rights reserved

CISO-Aligned Sales
by Mike Sobiegraj
Former long-time enterprise cyber executive. I help cybersecurity sales leaders win enterprise deals by applying my firsthand knowledge of what moves deals forward – and what doesn’t.
Free value
One-pager
One-pager
One-pager
Tool
Handbook
Legal stuff
© 2025-2026 Mike Sobiegraj. All rights reserved

CISO-Aligned Sales
by Mike Sobiegraj
Former long-time enterprise cyber executive. I help cybersecurity sales leaders win enterprise deals by applying my firsthand knowledge of what moves deals forward – and what doesn’t.
Free value
One-pager
One-pager
One-pager
Tool
Handbook
Legal stuff
© 2025-2026 Mike Sobiegraj. All rights reserved